
SAN FRANCISCO — Billions of gadgets—a lot of them already patched—are suffering from a Wi-Fi vulnerability that permits within sight attackers to decrypt delicate knowledge despatched over the air, researchers stated on Wednesday on the RSA safety convention.
The vulnerability exists in Wi-Fi chips made through Cypress Semiconductor and Broadcom, the latter a chipmaker Cypress obtained in 2016. The affected gadgets come with iPhones, iPads, Macs, Amazon Echos and Kindles, Android gadgets, Raspberry Pi three’s, and Wi-Fi routers from Asus and Huawei. Eset, the safety corporate that came upon the vulnerability, stated the flaw basically impacts Cyperess’ and Broadcom’s FullMAC WLAN chips, which can be utilized in billions of gadgets. Eset has named the vulnerability Kr00ok, and it’s tracked as CVE-2019-15126.
Producers have made patches to be had for many or all the affected gadgets, however it’s no longer transparent what number of gadgets have put in the patches. Of largest worry are prone wi-fi routers, which frequently move unpatched indefinitely.
“This leads to situations the place shopper gadgets which might be unaffected (both patched or the use of other Wi-Fi chips no longer susceptible to Kr00ok) may also be hooked up to an get right of entry to level (frequently instances past a person’s keep an eye on) this is prone,” Eset researchers wrote in a analysis paper revealed on Wednesday. “The assault floor is very much larger, since an adversary can decrypt knowledge that used to be transmitted through a prone get right of entry to level to a particular shopper (which might or will not be prone itself).”
A key consisting of all zeros
Kr00ok exploits a weak point that happens when wi-fi gadgets disassociate from a wi-fi get right of entry to level. If both the end-user tool or the get right of entry to level is prone, it is going to put any unsent knowledge frames right into a transmit buffer after which ship them over the air. Fairly than encrypt this information with the consultation key negotiated previous and used all the way through the standard connection, prone gadgets use a key consisting of all zeros, a transfer that makes decryption trivial.
Disassociation normally occurs when a shopper tool roams from one Wi-Fi get right of entry to level to every other, encounters sign interference, or has its Wi-Fi grew to become off. Hackers inside of vary of a prone shopper tool or get right of entry to level can simply cause disassociations through sending what’s referred to as control frames, which aren’t encrypted and require no authentication. This loss of safety lets in an attacker to forge control frames that manually cause a disassociation.
With the pressured disassociation, prone gadgets will normally transmit a number of kilobytes of information that’s encrypted with the all-zero consultation key. The hacker can then seize and decrypt the information. Eset researcher Robert Lipovsky advised me hackers can cause a couple of disassociations to additional the possibilities of acquiring helpful knowledge.
The next two diagrams assist illustrate how the assault works.
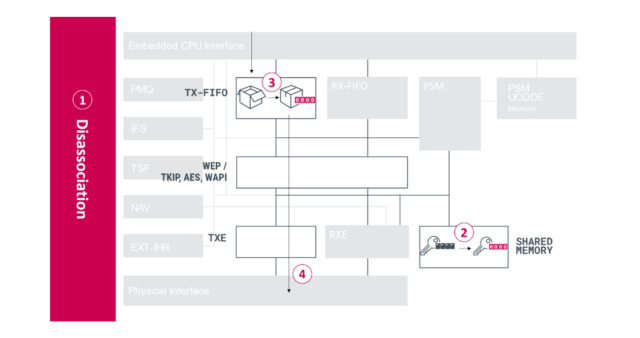
Eset
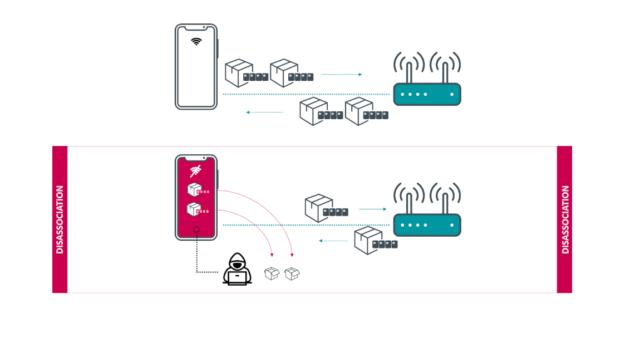
Eset
Eset researchers made up our minds that a number of gadgets are prone, together with:
- Amazon Echo 2d gen
- Amazon Kindle eighth gen
- Apple iPad mini 2
- Apple iPhone 6, 6S, eight, XR
- Apple MacBook Air Retina 13-inch 2018
- Google Nexus five
- Google Nexus 6
- Google Nexus 6S
- Raspberry Pi three
- Samsung Galaxy S4 GT-I9505
- Samsung Galaxy S8
- Xiaomi Redmi 3S
The researchers additionally discovered that the next wi-fi routers are prone:
- Asus RT-N12
- Huawei B612S-25d
- Huawei EchoLife HG8245H
- Huawei E5577Cs-321
An Apple spokesman stated the vulnerabilities had been patched ultimate October with main points for macOS right here and for iOS and iPadOS right here.
Producers of alternative prone gadgets that also obtain patch make stronger could not straight away be reached for remark.
The researchers examined Wi-Fi chips from different producers, together with Qualcomm, Realtek, Ralink, and Mediatek and located no proof any of them had been prone. Because it used to be not possible for the researchers to check all gadgets, it’s conceivable that different gadgets the use of Cypress and Broadcom chips also are affected.
Whilst the vulnerability is attention-grabbing and customers will have to be certain that their gadgets are patched temporarily—in the event that they aren’t already—there are some things that decrease the real-world danger posed. For something, maximum delicate communications in 2020 are already encrypted, in most cases with the delivery layer safety protocol or through different strategies. A evident exception to that is area title lookups, which, except a pc is the use of DNS over HTTPS or DNS over TLS, are despatched solely over plaintext. Hackers who considered those requests would be capable to be told what domains customers had been gaining access to.
Although a prone tool is speaking over HTTP or every other unencrypted channel, hackers may get better best a number of kilobytes of the information flowing over it at anyone time. It’s unsure attackers may time the disassociations in some way that may be certain that passwords or different delicate knowledge could be captured. That implies helpful assaults must contain a considerable amount of success or disassociations that happened again and again in fast succession.
It additionally turns out most likely that repeated assaults could be simple to locate since Wi-Fi connections would get started and prevent time and again without a transparent explanation why.
In spite of the restricted danger posed, readers will have to be certain that their gadgets have gained updates issued through the producers. This recommendation is maximum essential for customers of prone Wi-Fi routers, since routers are frequently onerous to patch and since prone routers depart communications open to interception even if shopper gadgets are unaffected or are already patched.



